The Lean Compliance Blueprint
Achieving Defensible Security Without the "Certification Tax"

In the modern regulatory landscape, “compliance” is no longer optional. Whether triggered by a new data protection law, a “Standard of Care” clause in a Tier-1 contract, or a supply-chain audit, small and mid-sized organizations are being forced to prove their security posture.
The industry’s standard response is to push for a formal ISO 27001 certification—a process that often costs upwards of $20,000 in audit fees alone, not including the hundreds of hours of internal labor. For many, this is a “Certification Tax” that drains resources without actually hardening the infrastructure.
There is a smarter, leaner way: The Defensible Compliance Model. This approach uses the governance structure of ISO 27001 to prove “Management Intent” while using the CIS 18 Benchmarks to provide the technical “Proof.” Here is how to build it in bite-sized, cost-conscious steps.
1. The Strategy: Why “Good Faith” is Your Best Defense
If a regulator or a major client audits your business, they are looking for one thing: Evidence of Due Diligence. By adopting the core components of ISO 27001—specifically the Risk Register and Management Review—you are demonstrating that security is a deliberate business process, not an IT accident. Even without a formal badge, presenting an ISO-aligned Risk Register shows a level of maturity that satisfies the “Reasonable Security” requirements found in most global regulations.
The Power of CIS 18 Benchmarks
While ISO 27001 tells you what to manage, it is notoriously vague on how. This is where the CIS 18 (Center for Internet Security) provides the muscle. By following the CIS Benchmarks, you aren’t just “doing security”; you are following a globally recognized, prescriptive technical standard. This makes your compliance “Defensible”—if a breach occurs, you can prove you followed industry-standard hardening guides.
2. The Implementation Roadmap: Bite-Sized & Free
You don’t need to spend $10,000 on GRC software to start. You can achieve high-quality compliance using free tools and disciplined documentation.
Phase 1: The Governance Foundation (Cost: $0)
The Risk Register: Identify the top 10 threats to your specific business (e.g., Ransomware, Data Leakage via SaaS, Physical Theft). Document the impact and your current mitigation strategy.
The Statement of Applicability (SoA): List which ISO 27001 controls apply to you. If a control doesn’t apply (e.g., Physical Security for a 100% remote team), document why. This proves to an auditor that you didn’t “ignore” it; you “assessed” it.
Quarterly Management Review: Hold a 30-minute meeting with leadership to review the Risk Register. Document the minutes. This fulfills the “Management Commitment” requirement that is often a make-or-break element in audits.
Phase 2: Technical Hardening (Cost: $500–$1,000)
Identity is the New Perimeter: Instead of an expensive firewall, invest your first $500 in a Business Password Manager (e.g., Bitwarden) and enforce Multi-Factor Authentication (MFA) on every single login. This single step mitigates the majority of common attacks.
Endpoint Encryption: Use built-in tools like BitLocker (Windows) and FileVault (macOS). It’s free, and it checks the box for “Data at Rest” protection required by almost every regulation.
The CIS Benchmark Hardening: Download the free CIS Benchmark PDFs for your specific stack (e.g., AWS, Microsoft 365, Windows 11). These provide the exact “Checklist” your IT person needs to harden the system.
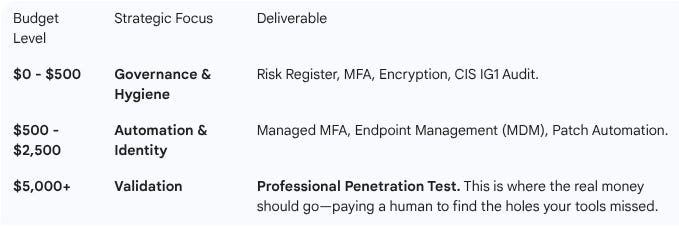
The “Sweet Spot” for ROI
The maximum ROI is found in the $500–$2,000 range. By spending money on Identity Management and Basic Automation, you eliminate the “Human Error” that causes 85% of breaches. Moving to a full ISO certification only makes sense when the Contract Value of a deal requiring it exceeds the Cost of Certification by at least 5x.
4. The “Make or Break” Elements
Even without a formal certificate, there are hurdles you cannot miss if you want to be “Compliant”:
Access Revocation: You must be able to prove that when an employee leaves, their access to everything is cut within 24 hours.
Incident Response: You need a one-page “Battle Plan” for what happens if you get hacked. If a client asks for this and you don’t have it, you fail the “Good Faith” test.
Vendor Management: You are responsible for your vendors. Having a simple “Security Questionnaire” for your sub-processors proves you are managing the entire data chain.
5. Summary: A Case for Discipline Over Dollars
Compliance isn’t about buying a product; it’s about maintaining a process. By using the ISO 27001 framework for management and the CIS 18 for technical execution, a small business can build a security posture that is:
Defensible in a legal or regulatory audit.
Scalable as the business grows.
Cost-Effective, focusing every dollar on actual risk reduction rather than audit paperwork.
This “Lean Compliance” model allows you to tell any prospect: “We operate to ISO 27001 standards and follow CIS 18 Benchmarks for all technical hardening. Here is our Risk Register and our most recent technical audit to prove it.” In 90% of cases, that transparency wins the deal.